In the vast landscape of digital networking, few elements are as fundamental as the IP address. It’s the unique identifier that allows devices to communicate across the internet, much like a postal address directs mail to the right doorstep. But what happens when an address doesn’t quite fit the rules? Enter 212.32.266.234, a sequence that looks deceptively like a standard IP but hides a subtle flaw. This article delves deep into the intricacies of IP addresses, using 212.32.266.234 as a lens to explore structure, validation, common pitfalls, and the broader implications for modern technology. We’ll unpack why this particular string sparks curiosity among tech enthusiasts and professionals, all while providing practical insights to enhance your understanding of networking basics.
The Fundamentals of IP Addresses
To appreciate the anomaly of 212.32.266.234, we first need to grasp what an IP address truly is. Internet Protocol (IP) addresses serve as the cornerstone of data transmission on the web. They come in two main versions: IPv4 and IPv6, with IPv4 being the older and more widely used format despite its limitations.
An IPv4 address consists of four numbers separated by periods, each ranging from 0 to 255. This range isn’t arbitrary; it’s rooted in binary representation. Each number, known as an octet, represents 8 bits, allowing for 256 possible values (2^8). Together, these four octets create over 4 billion unique combinations, which sounded ample in the early days of the internet but has since led to address exhaustion.
Consider how devices use these addresses. When you type a website URL into your browser, your computer translates it into an IP address via DNS (Domain Name System). Data packets then hop from router to router, guided by these numerical labels. Without strict adherence to the format, communication breaks down. That’s where examples like 212.32.266.234 become instructive—they highlight what goes wrong when the rules are bent.
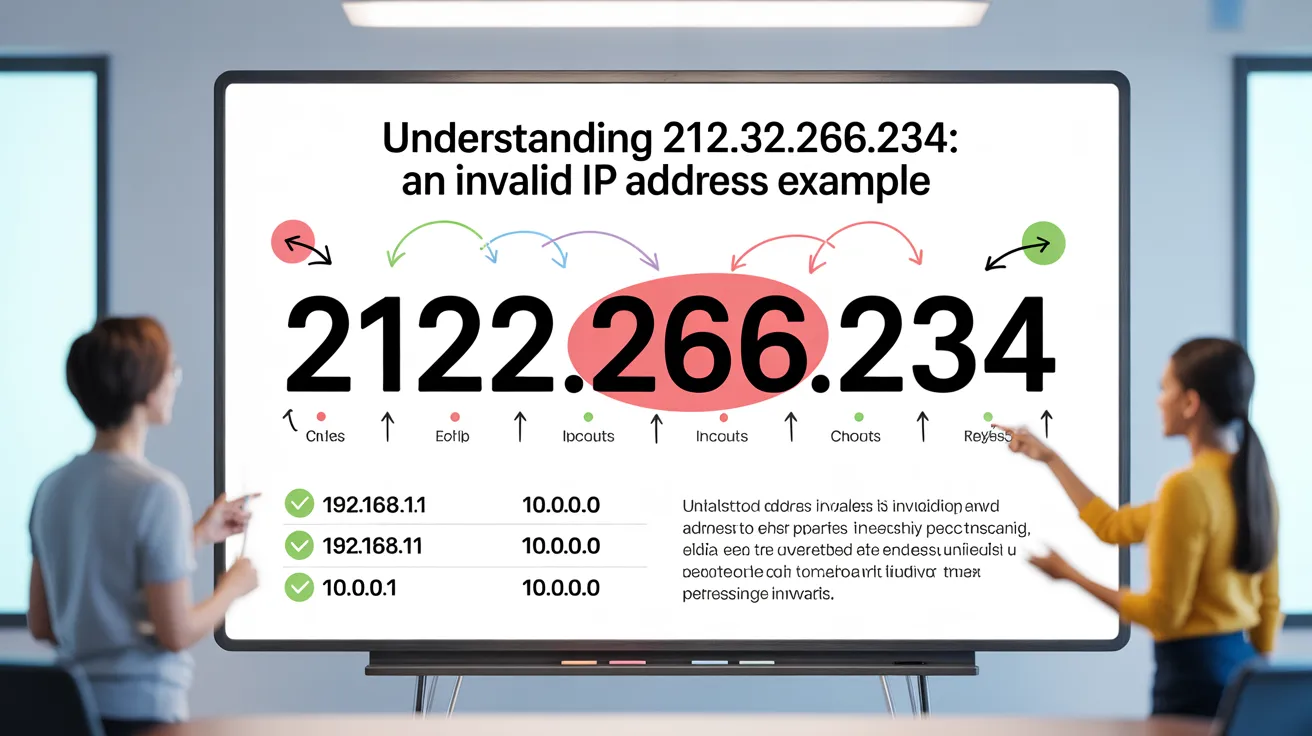
Breaking Down the Structure of 212.32.266.234
Let’s dissect 212.32.266.234 octet by octet to see why it doesn’t pass muster. The first octet, 212, falls within the valid range (0-255) and typically indicates a Class C address in traditional classifications, often assigned to networks in Europe or other regions managed by RIPE NCC. The second octet, 32, is also fine, suggesting a subnet within a larger block.
Now, the third octet: 266. Here’s the issue. In binary terms, 255 is 11111111, the maximum for 8 bits. 266 would require at least 9 bits (100001010 in binary), which overflows the octet boundary. This makes 212.32.266.234 inherently invalid as an IPv4 address. The fourth octet, 234, is valid on its own, but the whole string fails due to that single overreach.
Why might someone encounter 212.32.266.234? It could stem from a typing error, a misconfigured script, or even intentional use in testing scenarios. In programming, for instance, developers might input such values to check how their applications handle edge cases. If software doesn’t validate inputs properly, it could lead to unexpected behavior, like failed connections or security loopholes.
| Octet Position | Value in 212.32.266.234 | Valid Range | Status | Notes |
|---|---|---|---|---|
| First | 212 | 0-255 | Valid | Often part of public IP blocks |
| Second | 32 | 0-255 | Valid | Subnet identifier |
| Third | 266 | 0-255 | Invalid | Exceeds maximum by 11 |
| Fourth | 234 | 0-255 | Valid | Typical host identifier |
This table illustrates the breakdown, showing how one errant value invalidates the entire address. Tools like ping or traceroute would reject 212.32.266.234 outright, preventing any network interaction.
Common Mistakes Leading to Invalid IPs Like 212.32.266.234
Invalid addresses such as 212.32.266.234 don’t appear out of thin air. They often result from human error or systemic issues. For beginners setting up home networks, mistyping an octet—say, confusing 255 with 266—can halt connectivity. In enterprise environments, automated scripts pulling data from databases might concatenate numbers incorrectly, producing anomalies.
Another frequent culprit is confusion between IPv4 and other notations. Some might mistake hexadecimal values for decimal, where ‘FF’ (255) could be misentered as a higher number. Additionally, in virtual private networks (VPNs) or cloud setups, misconfigurations in DHCP servers can distribute flawed addresses, though safeguards usually catch them.
To avoid these pitfalls, always double-check inputs. Use validation libraries in code: In Python, for example, the ipaddress module can quickly flag 212.32.266.234 as invalid with a simple try-except block. For manual checks, remember the octet rule and verify against known ranges for private vs. public IPs.
How to Validate IP Addresses Effectively
Validation is key to preventing issues with strings like 212.32.266.234. Start with basic checks: Split the string by dots and ensure exactly four parts. Then, confirm each is an integer between 0 and 255, inclusive. Advanced validation might include checking for reserved addresses (e.g., 0.0.0.0 or 127.0.0.1) or multicast ranges (224-239).
Software tools abound for this. Online validators let you input 212.32.266.234 and receive instant feedback. In scripting, regular expressions (regex) like ^((25[0-5]|2[0-4][0-9]|[01]?[0-9][0-9]?).){3}(25[0-5]|2[0-4][0-9]|[01]?[0-9][0-9]?)$ can match valid IPv4 patterns. But regex alone isn’t foolproof; combine it with numerical checks for robustness.
For network admins, tools like Wireshark can monitor traffic and spot invalid attempts. Educating teams on examples like 212.32.266.234 fosters a culture of precision, reducing downtime and enhancing security.
| Validation Step | Description | Example Check for 212.32.266.234 | Result |
|---|---|---|---|
| Count Octets | Ensure four segments separated by dots | 212.32.266.234 has four | Pass |
| Integer Conversion | Convert each to int | Third octet: int(‘266’) = 266 | Pass (but next fails) |
| Range Check | 0 <= value <= 255 | 266 > 255 | Fail |
| Leading Zeros | Avoid invalid formats like 012 | No issues here | Pass |
| Overall Validity | Combine all | Fails due to range | Invalid |
This step-by-step table provides a practical framework you can apply to any suspected IP.
Security Implications of Invalid Addresses
While 212.32.266.234 itself poses no direct threat, invalid IPs can signal bigger problems. In cybersecurity, attackers might inject malformed addresses into logs or inputs to exploit buffer overflows or crash systems. If an application blindly accepts 212.32.266.234, it could lead to denial-of-service attacks or data leaks.
On the flip side, robust validation protects against such vectors. Firewalls often drop packets with invalid sources, but edge cases like 212.32.266.234 test their efficacy. In penetration testing, ethical hackers use similar invalid formats to probe weaknesses, ensuring networks are resilient.
Consider real-world scenarios: A misconfigured router attempting to route to 212.32.266.234 would loop or fail, alerting admins to issues. This underscores the need for layered security—combine IP validation with intrusion detection systems for comprehensive defense.
The Shift to IPv6 and Beyond
As IPv4 addresses dwindle, IPv6 emerges as the future, with its 128-bit format offering trillions of possibilities. Unlike 212.32.266.234, IPv6 uses hexadecimal notation (e.g., 2001:db8::ff00:42:8329), eliminating octet limits but introducing new complexities.
Transitioning involves dual-stack setups, where devices handle both versions. For invalid IPv4 like 212.32.266.234, IPv6 equivalents might involve improper colons or abbreviations, but the expanded space reduces exhaustion risks. Experts predict full IPv6 adoption will minimize reliance on quirky examples like 212.32.266.234, focusing instead on scalability.
Case Studies: Real-World Encounters with Similar Anomalies
Though 212.32.266.234 is hypothetical, similar invalid IPs have caused notable incidents. In one software bug report, a developer input 192.168.256.1 (invalid octet), crashing a server farm. Lessons learned: Always implement input sanitization.
Another case involved a typo in a config file, turning 10.0.0.255 into 10.0.0.256, isolating an entire subnet. Quick validation scripts resolved it, but downtime cost thousands. These stories illustrate how understanding 212.32.266.234-like errors prevents larger failures.
In educational settings, instructors use 212.32.266.234 to teach binary math. Students calculate why 266 overflows, reinforcing concepts like bit shifting and subnetting.
Advanced Topics: Subnetting and Beyond 212.32.266.234
Diving deeper, subnetting divides IP blocks using masks. For a valid counterpart like 212.32.255.234/24, it defines a network of 256 hosts. But with 212.32.266.234, subnet calculations fail from the start.
Explore CIDR notation, where variable masks optimize allocation. Invalid entries disrupt this, emphasizing clean data in routing tables.
For hobbyists, experimenting with virtual machines can simulate scenarios. Try pinging 212.32.266.234 in a safe environment—it’ll error out, teaching command-line diagnostics.
Conclusion
212.32.266.234 serves as a compelling reminder of the precision required in digital addressing. By examining its invalid nature, we’ve covered the essentials of IP structure, validation techniques, security considerations, and the evolving landscape toward IPv6. Whether you’re a novice troubleshooting your home Wi-Fi or a seasoned engineer designing enterprise networks, recognizing patterns like 212.32.266.234 equips you to navigate challenges with confidence. The internet thrives on rules, and bending them, even accidentally, reveals the system’s ingenuity. Stay curious, validate rigorously, and keep your connections strong.


Leave a Reply